Adobe Commerce empowers businesses to support multiple storefronts for various brands, product lines, or geographic regions, all from a single platform and managed through a single administrative interface. Its robust, multisite architecture and advanced catalog service allow for rapid expansion into new markets while managing millions of SKUs across brands and regions. The platform enhances efficiency by enabling shared use of branding, catalogs, content, promotional offers, and other resources across stores. However, each store can also be completely customized to align with specific brand identities or regional demands, with native support for multiple languages, currencies, and tax regulations. Moreover, extensive APIs and integration starter kits streamline the customization of functionality and the integration of essential back-office systems across your organization, ensuring you can address a wide range of operational needs.
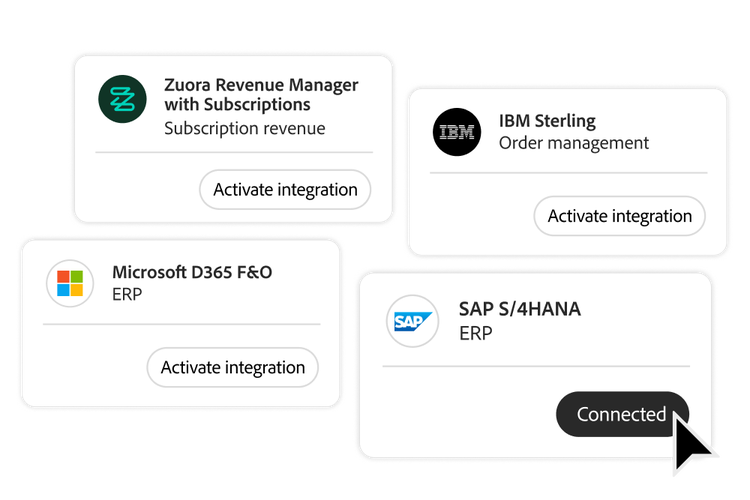
Adobe Commerce seamlessly connects with any back-office system, including enterprise resource planning (ERP), customer relationship management (CRM), product information management (PIM), warehouse management systems (WMS), and order management systems (OMS), ensuring smooth and efficient ecommerce experiences. To reduce the time it takes to integrate with back-office systems, Adobe Commerce provides an integration starter kit featuring a set of templates, onboarding scripts, and architectural best practices. This kit simplifies data synchronization for key objects like orders, customers, inventory, products, and shipping status between Adobe and third-party systems. Additionally, prebuilt connectors are available through
Adobe Exchange to further accelerate integration with solutions, such as IBM Sterling Order Management, Microsoft Dynamics 365 ERP, SAP S4/HANA ERP, and more.
Adobe Commerce incorporates cutting-edge AI-powered merchandising tools designed to deliver personalized ecommerce experiences that significantly enhance sales and conversion rates. The platform uses AI-powered semantic search to understand the meaning and intent behind each search to deliver fast and relevant search results tailored to customers’ on-site behavior and product popularity such as most viewed, most added to cart, most purchased, trending, and more. AI also organizes products on category pages to maximize sales. To enhance product discovery, Adobe Commerce includes 13 types of AI-powered product recommendations, using insights from customer history, frequently paired items, visual similarities, and trending products to drive conversion and average order values. The solution also includes agentic content and image generation capabilities, making it faster and easier to create variations for more personalized commerce experiences.
Adobe Commerce enables brands to harness agentic commerce capabilities that drive product discovery, engagement, and conversions while boosting operational efficiency. Customers can enhance product discovery and sales on AI-native channels with Adobe Commerce Integration into Adobe LLM Optimizer and through support for emerging agentic commerce protocols from Google, OpenAI, and others. AI-powered conversations via the Adobe Commerce Integration into Adobe Brand Concierge help customers find what they want faster by matching customer intent to accurate, real-time product catalog information and brand-approved content. Adobe Commerce also provides developer agents to accelerate app development, customizations, and storefront or extension migrations, helping brands go to market faster.
Adobe Commerce runs on an auto-scaling, highly available multicloud platform that can easily handle flash sales with over 200,000 orders per hour. The SaaS-based catalog service from Adobe helps to accelerate page load times on category, product detail, and search pages with 10x faster data retrieval and efficient synchronization with third-party systems, such as ERPs. Adobe Commerce also provides monitoring tools that track over 200 metrics to help maintain site health and performance.
Consumers and B2B buyers trust you with their sensitive data, and Adobe Commerce helps you maintain that trust with industry-leading security measures. Certified as a PCI (payment card industry) Level 1 Solution Provider, the platform undergoes regular security testing, including penetration tests and vulnerability assessments, verified by third-party vendors. Web application firewalls (WAF) use advanced AI-powered threat detection to provide comprehensive protection against a broad range of vulnerabilities. Adobe Commerce cloud-based solutions provide content delivery network (CDN) and distributed denial of service (DDoS) protection. An included security scan tool helps your teams proactively monitor their sites and receive alerts about known security risks, malware, and unauthorized access. If your business handles sensitive electronic personal health information, Adobe Commerce offers a HIPAA-ready solution for Adobe Commerce on Cloud with enhanced privacy, security, and governance controls.
Adobe Commerce simplifies global expansion with a flexible multisite architecture and built-in localization features. Businesses can easily model their catalog for multiple markets and craft region-specific sites with native support for multiple languages, currencies, and tax regulations. Multiple inventory locations can be configured to maintain accurate stock levels across regions, and prebuilt extensions make it easy to integrate with local payment and shipping options. A global cloud infrastructure enables in-region hosting, while an extensive network of experts and developers provides reliable support to facilitate your expansion efforts.
Adobe delivers the highest level of support to equip your teams with the technical expertise and strategic guidance they need to drive business growth. With 24/7 access to expert assistance, teams can quickly troubleshoot and resolve issues. Account managers and advisory teams provide assistance with planning, best practices, and maximizing platform value. Your teams also have access to extensive resources — including comprehensive documentation, tutorials, code samples, a developer playground, and community forums available through
Adobe Experience League and
Adobe Developer to accelerate your time to market and optimize platform usage. An extensive network of experienced partners and developers further supports digital commerce strategy, implementation, and long-term maintenance.
Adobe Digital Learning Services provides both instructor-led and on-demand courses designed to help your team quickly master the essentials. Courses cover key topics such as development fundamentals, building and managing online stores, and effectively managing catalogs and products within Adobe Commerce.